Identity Management Platform Showdown: Which SSO and IAM Solution Works Best for UK Businesses
Comparing Okta, Microsoft Entra ID, Google Identity, JumpCloud and open source IdP platforms for UK businesses. Real pricing, security track records, and which fits.
Alan Avins
Stabilise

Your business has outgrown shared passwords and "please email IT for access" chaos. You know you need single sign-on, proper multi-factor authentication, and automated user provisioning. But which platform do you choose when every vendor claims to be "enterprise-grade" and "seamlessly integrated"?
This is the comparison article I wish existed when evaluating identity platforms for London businesses. No marketing fluff, no vendor bias, just the actual trade-offs between the platforms UK SMEs deploy.
What We're Comparing (And Why These Specific Platforms)
Commercial platforms:
- Microsoft Entra ID (formerly Azure AD) – because you probably already have it
- Okta Workforce Identity – the most common "vendor-neutral" choice
- Google Cloud Identity – for Google Workspace shops
- JumpCloud – increasingly popular with MSPs and Mac-heavy businesses
- OneLogin – mid-market alternative to Okta
- Ping Identity – enterprise and regulated industries
- Auth0 (now Okta Customer Identity Cloud) – developer-focused, B2C angle
Open source options:
- Keycloak – the established self-hosted choice
- Authentik – modern, DevOps-friendly alternative
- Authelia – lightweight SSO gateway
- Zitadel – cloud-native identity platform
- Gluu – enterprise-grade open source
I'm not covering every niche player. These platforms represent what you'll encounter when speaking with IT consultancies, MSPs, and your peer businesses.
The Comparison Tables
Major Commercial Identity Platforms
Platform
Typical UK Pricing
Best For
Protocols
MFA & Passwordless
HR Integration
Deployment
Security Track Record
Microsoft Entra ID
Free tier included; P1 £4.80/user/month, P2 £7.20/user/month, Entra Suite £9.60/user/month
Businesses already on Microsoft 365 who want integrated identity, conditional access, and device management
SAML, OIDC, OAuth 2.0, WS-Fed; tight Microsoft integration plus broad SaaS support
Microsoft Authenticator, SMS, phone, conditional access, risk-based policies, FIDO2, Windows Hello
Azure AD Connect for on-prem AD; SCIM and app gallery; HR-driven provisioning requires configuration
Cloud-native (Azure), deeply integrated with Windows and Intune; hybrid AD scenarios work well
Massive enterprise footprint, mature security engineering; no catastrophic single breach like some competitors
Okta Workforce Identity
SSO from £1.60/user/month, bundles typically £4.80-6.40/user/month, higher tiers to £12/user/month
Multi-SaaS environments, businesses wanting vendor-neutral identity, MSPs standardising across clients
SAML, OIDC, OAuth 2.0, WS-Fed; massive pre-built app catalogue
Strong MFA with app, SMS, WebAuthn/FIDO2, contextual and adaptive policies; good passwordless support
Mature SCIM provisioning, broad HRIS integrations (Workday, BambooHR, etc.), sophisticated lifecycle automation
SaaS only, globally hosted; agents for on-prem AD/LDAP and VPN/RADIUS
Multiple high-profile breaches 2022-2024 (support system, session tokens); strong response process but reputation damaged
Google Cloud Identity
Free tier; Premium typically £1.60-6.40/user/month depending on bundle and features
Google Workspace organisations, browser-first businesses, ChromeOS environments
SAML, OIDC, OAuth 2.0; good catalogue for popular SaaS
Built-in MFA (app, SMS, security keys), strong FIDO2/passkey support, phishing-resistant
Basic SCIM and app provisioning; some HR integrations via partners; less sophisticated than Okta/Entra
SaaS only (Google Cloud); excels in browser-first environments
Solid track record, focus on secure-by-default and FIDO2; most incidents relate to misconfiguration rather than platform breaches
JumpCloud
Typically £3.20-4.80/user/month for directory + SSO bundles
Mac/Windows/Linux mixed fleets, cloud-first SMBs, businesses moving away from traditional AD
SAML, OIDC, LDAP-over-SSL, RADIUS; replaces or augments AD
Built-in MFA with TOTP/app and device-context policies
User lifecycle to SaaS apps and endpoints; not as deep HRIS integration as Okta but strong device focus
Cloud directory-as-a-service with agents on endpoints and servers; good for remote teams
Generally positive security reputation in SMB/MSP circles; smaller footprint means fewer headline incidents
OneLogin
SSO around £3.20/user/month; higher tiers add MFA, directory, advanced features
Mid-market businesses wanting simpler SSO/MFA without full Okta complexity
SAML, OIDC, OAuth 2.0, AD/LDAP integration
Strong MFA (SMS, app, biometrics, hardware tokens); good policies but less breadth than Okta/Entra
Supports SCIM, directory sync, some HRIS links; adequate for most SME needs
SaaS-first; on-prem agents for AD/LDAP and VPN
Serious breach in 2017; improved since but some security teams still consider history during evaluation
Ping Identity
Enterprise pricing, typically mid-to-high single digits per user/month
Complex hybrid/legacy environments, large enterprises, financial services, regulated industries
Very broad: SAML, OIDC, OAuth 2.0, WS-Trust, WS-Fed, legacy federation protocols
Full MFA and adaptive authentication; strong in regulated environments
Strong lifecycle and governance, especially with broader Ping suite
SaaS (PingOne) plus on-prem components; good for phased migration from legacy
Longstanding enterprise vendor with strong compliance story; no widely publicised Okta-scale incidents in recent years
Auth0 (Okta Customer Identity Cloud)
Free to 7,500 monthly active users; paid from £28/month for 500 MAUs, scales with volume
Developer-first customer identity, B2C/B2B application authentication where you control UX
SAML, OIDC, OAuth 2.0; very flexible rules and hooks model
Rich MFA options, adaptive controls, passwordless, WebAuthn
SCIM and custom logic for provisioning; more app-centric than HR-centric
SaaS; integrate via SDKs and APIs
Now under Okta's security umbrella (pros and cons); also discussions about hidden costs (per-IdP connection fees)
Open Source and Self-Hosted Platforms
Platform
Typical Cost Model
Best For
Protocols
MFA & Passwordless
Provisioning
Deployment
Security Considerations
Keycloak
Software free; you pay infrastructure and operations (or Red Hat support)
Self-hosted SSO/IdP for enterprises wanting full control and extensibility
SAML, OIDC, OAuth 2.0; IdP brokering, social logins
MFA with TOTP, WebAuthn, SMS/email via plugins; passwordless via extensions
User federation to LDAP/AD; provisioning via REST/SCIM and custom code; HR integrations require engineering
Self-host (VMs, containers, Kubernetes) or managed by third parties
Mature and widely used; security depends on patching and configuration but benefits from open source scrutiny
Authentik
Free core; optional paid support/hosting from vendors
Modern, DevOps-friendly self-hosted IdP for homelab to mid-size organisations
SAML, OIDC, OAuth 2.0, LDAP proxy; reverse-proxy style app protection
TOTP and WebAuthn support; policy-driven flows; passwordless via WebAuthn
Provisioning via APIs, directory sync, Terraform; HRIS is build-it-yourself
Containers/Kubernetes, with Helm charts
Younger than Keycloak but rapidly evolving; active community and transparent issue handling
Authelia
Free; you pay infrastructure and operations
SSO/MFA gateway for self-hosted web apps; strong in homelab and SMB self-hosting
Primarily sits in front of apps via reverse proxy; supports OIDC/SAML in newer versions
Strong MFA (TOTP, WebAuthn, Duo); focuses on hardening access to internal apps
Very limited built-in provisioning; more an access gateway than full IAM
Self-host only, often with Nginx/Traefik; configuration-as-code
Good security posture for those comfortable with infrastructure-as-code; still niche versus Keycloak
Zitadel
Free community edition; paid cloud tiers and enterprise support
Cloud-native identity platform aiming to be managed open source alternative to Auth0/Okta
OIDC, OAuth 2.0; SAML via integrations; multi-tenant and B2B-friendly
Built-in MFA and passwordless with FIDO2/WebAuthn
Organisation and user management, some provisioning APIs; still maturing compared to Keycloak
Self-host on Kubernetes or use hosted Zitadel cloud
Active development with security transparency; smaller install base than Keycloak
Gluu
Community edition free; enterprise subscriptions for support and extras
Enterprise-grade open source IAM for organisations needing SSO + strong MFA + governance
SAML, OIDC, OAuth 2.0; strong federation support
MFA with OTP, FIDO2/WebAuthn, SMS and more
SCIM-based provisioning and directory integrations; can underpin complex identity architectures
Self-hosted (various topologies) or managed by Gluu/partners
Longstanding open source IAM; solid reputation in communities that adopt it but requires specialist skills
What This Means For Your Specific Situation
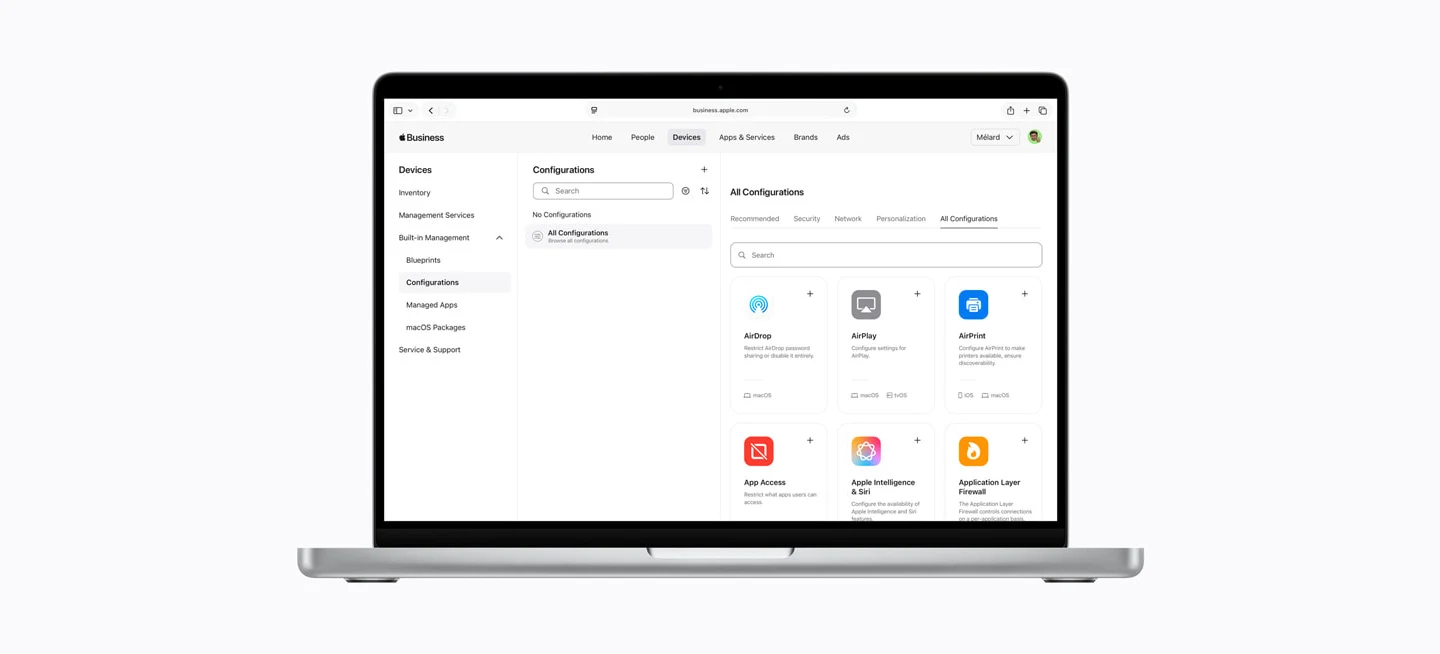
Mac-Heavy SMEs on Microsoft 365
Best three choices:
Platform
Why It Works
Key Benefits
Cost Reality
Microsoft Entra ID
You already own core identity with Microsoft 365; Business Premium + new security add-ons bring enterprise-grade identity into SME budgets
Conditional Access, Identity Protection, risk-based policies; integrates with Intune for Mac device management; maximise what you're already paying for
Core features bundled with M365; P1/P2 tiers give enterprise controls at SME-friendly prices
JumpCloud
Directory-as-a-service that treats Macs as first-class citizens; good for mixed fleets and remote teams without running on-prem AD
Unified user and device management (Mac/Windows/Linux), SSO from one console; device-centric rather than purely Microsoft-centric
Typically cheaper than full Entra P2 + Intune stack for Mac-heavy fleets; per-user pricing in low-to-mid single digits works for 50-300 seats
Okta Workforce Identity
Best when you're on Microsoft 365 but live in dozens of non-Microsoft SaaS apps; shines for complex SaaS estates
Huge app catalogue, strong SCIM provisioning, flexible workflows; easy to integrate Microsoft 365 alongside other platforms
More expensive than "turning up" Entra features, but earns its keep with time saved on integrations and automation
When to pick which:
- Choose Entra ID only if you're all-in on Microsoft 365, mostly browser/SaaS-based, and happy to manage Macs via Intune
- Add or prefer JumpCloud if you want device-centric cloud directory that treats Macs as equals while still integrating with Microsoft 365
- Bring in Okta if you have complex multi-SaaS needs, want HR-driven provisioning at scale, or operate as an MSP standardising identity across clients
Mac-Heavy SMEs on Google Workspace
Best three choices:
Platform
Why It Works
Key Benefits
Cost Reality
Google Workspace Identity
Uses identities you already have; ideal if you're all-in on Gmail, Drive, Meet and mostly browser-based SaaS
Built-in SSO to many apps, MFA with Google Authenticator and security keys, strong passkey/FIDO2 support; works great on Chrome + macOS
Essentially included in Workspace subscription; best TCO if you don't need deep HRIS provisioning or device-level policies
JumpCloud
Strategic partnership with Google Workspace positions it as modern replacement for AD/Entra/Intune in Google environments
Cloud directory + SSO + device management from one console; richer MFA, conditional access and device posture than Google SSO alone
Per-user pricing attractive for 50-300 seats; saves cost versus separate AD, Intune and MDM stacks
Okta Workforce Identity
Excellent when you run Google Workspace but rely on lots of non-Google SaaS and want vendor-neutral control with advanced automation
Deep integration with Google Workspace directory; 8,000+ app catalogue, powerful SCIM provisioning, adaptive MFA beyond Google's group-based model
Higher price point but pays off in larger SaaS estates where automation and governance save admin time
When to pick which:
- Go Google-only if you're small-to-mid Google-native shop, mostly browser-based, and happy with straightforward SSO/MFA
- Add JumpCloud when you want strong Mac device management plus unified directory and SSO without Microsoft tooling
- Bring in Okta when you've grown into complex multi-SaaS environment or need richer HRIS-driven provisioning than Google can provide
Windows-First SMEs on Microsoft 365
Best three choices:
Platform
Why It Works
Key Benefits
Cost Reality
Microsoft Entra ID + Intune
Native identity and device combination for Windows; feels like extension of existing M365 rather than bolt-on
Hybrid AD/Entra support, Conditional Access, device compliance, Defender integration, Autopilot, Windows security baselines
Core Entra included with most M365 plans; Business Premium + security add-ons give P1-style features at SME prices, usually cheaper than third-party IdP plus separate UEM
Okta Workforce Identity
Ideal where you're Windows-on-365 but live in large multi-SaaS world and want app-centric identity with advanced lifecycle
Huge app catalogue, strong SCIM provisioning, adaptive MFA; supports Microsoft 365 as one of many apps with AD/Entra underneath
Sits on top of Entra/AD rather than replacing; higher per-user cost justified when SaaS sprawl and compliance demand automation
JumpCloud
Good when you want to modernise away from on-prem AD but still have lots of Windows endpoints
Cloud directory plus cross-platform device management; acts as primary directory instead of AD, reducing domain controller footprint
Attractive pricing for 50-500 seats; may be cheaper than running AD + Entra P2 + Intune + VPN stack for distributed workforces
Windows-First SMEs on Google Workspace
Best three choices:
Platform
Why It Works
Key Benefits
Cost Reality
JumpCloud
Frequently recommended as "missing directory" for Google organisations with Windows laptops; replaces traditional AD
Cloud directory + full UEM for Windows/macOS/Linux; policies for BitLocker, patching and security baselines without servers
Low-to-mid single-digit per-user pricing compelling versus standing up AD, VPN and separate MDM; strong TCO for 50-500 seat remote Windows teams
Google Workspace Identity
Fine for very simple Windows environments using mostly browser-based apps
Integrated Google SSO, MFA and passkeys, Chrome and browser-centric controls; basic endpoint management suitable for lightweight Windows management
Essentially included in Workspace cost; lowest TCO but you sacrifice richer endpoint posture and software deployment
Okta Workforce Identity
Best where your Windows-on-Google organisation has big multi-SaaS footprint and wants sophisticated SSO and governance
Deep Google Workspace integration for directory sync, broad SAML/OIDC coverage, adaptive MFA; can combine with JumpCloud if you need more endpoint control
Higher per-user cost than Google-only or JumpCloud, but pays off when compliance, auditability and SaaS sprawl are main pain points
The Security Track Record Question
Let's address this directly because it matters.
Okta has had multiple high-profile incidents since 2022, including their support system compromise and session token access issues. These weren't minor configuration problems. They were significant breaches that affected customer environments. Okta publishes advisories and has strong response processes, but the frequency raises questions.
Does this mean you shouldn't use Okta? Not necessarily. It means:
- Implement zero-trust architecture regardless of your IdP
- Maintain comprehensive logging and monitoring
- Have incident response procedures that assume your IdP could be compromised
- Consider whether you need the vendor-neutral layer Okta provides, or whether staying closer to your primary platform (Microsoft/Google) reduces attack surface
Open source platforms share the same protocol-level risks as commercial options. SAML, OIDC and OAuth 2.0 all have known vulnerability classes. The difference is you're responsible for staying on top of security advisories and patches. If you lack in-house expertise for this, self-hosted identity becomes a liability rather than an asset.
Microsoft and Google benefit from massive security engineering teams and are under constant scrutiny. They've had incidents (every large platform has) but nothing approaching Okta's recent run. This matters when you're trusting a platform with every login to every system your business uses.
The Hidden Costs Nobody Mentions
Commercial platforms:
- Auth0 charges per identity provider connection in some tiers. If you want to federate with multiple external IdPs, costs escalate quickly.
- Okta's pricing looks reasonable until you add governance, advanced MFA, and API access management. The jump from base SSO to full enterprise suite is significant.
- Microsoft bundles identity with other services, which looks cheap until you realise you're paying for M365 E3/E5 to get features that come standard in dedicated IdPs.
Open source platforms:
- The software is free. Your time configuring, securing, patching and maintaining it is not.
- Keycloak running well requires understanding of Java, databases, load balancing, and identity protocols. Budget for this expertise.
- When something breaks at 3am, there's no support line. There's documentation, community forums, and your own technical capability.
The real cost question: What's your time worth? A £6/user/month SaaS IdP for 100 users costs £7,200 annually. If self-hosting Keycloak "saves" you that cost but requires 40 hours of senior engineer time over the year, you've not actually saved anything. You've just moved the cost from your software budget to your salary budget.
What We Recommend
At Stabilise, we typically deploy one of three approaches depending on the business:
For most Mac-heavy London businesses on Microsoft 365: Start with Entra ID P1 or P2. You're already paying for Microsoft 365, the integration with Intune works properly, and conditional access policies give you the control you need. Add JumpCloud if your Mac fleet needs richer device management than Intune provides.
For Google Workspace organisations under 100 users: Use Google's built-in identity and SSO. It works, it's included, and the complexity of adding another layer isn't justified unless you have specific compliance requirements or dozens of third-party SaaS applications.
For businesses with complex SaaS estates or regulatory requirements: Okta or Ping Identity, despite the higher cost and Okta's security history. The provisioning automation, governance capabilities, and vendor-neutral positioning justify the investment when you're managing 50+ applications or need detailed audit trails for compliance.
We don't recommend self-hosted identity platforms for most SMEs. The exception is if you already have strong in-house Linux/Kubernetes expertise and specific requirements that commercial platforms can't meet. Even then, Keycloak-as-a-service from a specialist provider is often smarter than running it yourself.
Questions to Ask Yourself
Before choosing a platform:
Do you need a separate IdP? If you're all-in on Microsoft 365 or Google Workspace with simple needs, you might not. The identity tools built into those platforms handle SSO, MFA and basic provisioning adequately for many businesses.
What's your source of truth for identity? If it's your HRIS system (BambooHR, Workday, etc.), you need strong lifecycle automation. If it's your email system, simpler SSO might be adequate.
How many SaaS applications do you use? Three applications don't justify Okta. Thirty probably do.
What's your team's technical capability? Self-hosted platforms require expertise. SaaS platforms require budget. Know which constraint binds tighter.
What happens when your IdP is compromised? This isn't theoretical anymore. Your answer should inform your architecture regardless of which platform you choose.
The Honest Answer
There's no single "best" identity platform. There's the platform that matches your environment, technical capability, budget, and risk tolerance.
If you're a 50-person London creative agency running entirely on Google Workspace with ten SaaS applications, Google's built-in identity tools are probably adequate. Adding Okta would be architectural complexity for no meaningful gain.
If you're a 200-person professional services firm on Microsoft 365 with 40 SaaS applications, strict compliance requirements, and people joining and leaving every month, you need sophisticated provisioning and governance. Entra ID P2 or Okta becomes justified.
If you're an MSP managing identity for dozens of clients across different platforms, JumpCloud's multi-tenant architecture and broad protocol support might be your best option regardless of what any comparison table says.
The platforms in these tables all work. They're all deployed successfully in thousands of businesses. Your job isn't to find the "best" one in abstract. It's to find the one that solves your specific problems without creating new ones.
Frequently Asked Questions
What is SSO and why does my business need it?
Single sign-on lets your team log in once to access all their business applications securely. It eliminates password fatigue, reduces help desk tickets for password resets, and gives IT visibility into who is accessing what. For businesses using more than a handful of SaaS tools, SSO significantly improves both security and productivity.
Which identity platform is best for Mac-heavy businesses?
For Mac-heavy businesses on Microsoft 365, start with Microsoft Entra ID and add JumpCloud if you need richer Mac device management. If you run Google Workspace, JumpCloud is often the strongest choice because it treats Macs as first-class citizens. Okta becomes worthwhile when you have a complex SaaS estate with dozens of applications.
Is Okta still safe to use after its security breaches?
Okta has had multiple high-profile incidents since 2022, which raised legitimate concerns. The platform remains widely deployed and has strong response processes. If you choose Okta, implement zero-trust architecture, maintain comprehensive logging, and have incident response procedures that assume your identity provider could be compromised.
Do small businesses need a separate identity platform?
Not always. If you are under 50 users and fully committed to Microsoft 365 or Google Workspace with simple needs, the built-in identity tools may be sufficient. A separate identity platform becomes valuable when you use more than ten SaaS applications, need HR-driven provisioning, or face compliance requirements.
What is the difference between Entra ID and JumpCloud?
Microsoft Entra ID is tightly integrated with Microsoft 365 and works best in Microsoft-centric environments. JumpCloud is a cloud directory service that treats Mac, Windows, and Linux devices equally, making it popular with mixed-fleet businesses and remote teams that want to avoid on-premises Active Directory.
Should we use an open-source identity platform to save money?
For most SMEs, no. Self-hosted platforms like Keycloak require expertise in Java, databases, and identity protocols. The software is free but the engineering time for setup, patching, and troubleshooting is not. A commercial platform at £6 per user per month for 100 users costs £7,200 annually, which is often less than the engineering time you would spend maintaining a self-hosted solution.
How do I choose between Microsoft Entra ID P1 and P2?
P1 covers conditional access and basic identity protection, which is enough for many businesses. P2 adds risk-based policies, privileged identity management, and access reviews. If you operate in a regulated industry or handle sensitive data, P2 is worth the extra cost. For straightforward office environments, P1 is usually sufficient.
What hidden costs should I watch for with identity platforms?
Auth0 charges per identity provider connection in some tiers, which escalates quickly if you federate with multiple external providers. Okta's jump from base SSO to enterprise features is steep. Microsoft bundles identity with broader licences, so you may pay for M365 E3 or E5 just to unlock specific identity features that come standard in dedicated platforms.